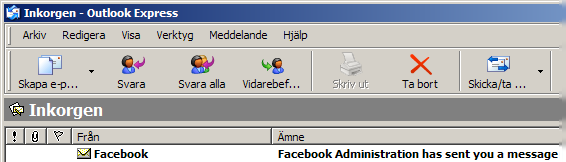
That spammers are working hard to pump out spam looking like legitimate email communication, from sites such as Facebook, is evident as the antivirus alerts increase in volume. However any alert recipient should be able to avoid being fooled by such spam with doing a few simple quick checks.
The first check is the easiest one to do. Is the email address to which the "official message" was sent actually the email that was registered on Facebook?
If it isn't then it is evidently a spam message sent from a spammer expecting a little bit of luck or a thick recipient. However if it is, there are a few more tests to do.

The devil is in the details, and popping the hood to look into the properties is a great way to drill deeper into data that typically reveals a lot of interesting data on where the email came from.
By checking the sending IP and name of the sending device a vast majority of spam can be detected, however this requires a bit more knowledge on the user side. A dead giveaway is if there is a return-path that goes elsewhere, and in many cases SPF responses other than "Pass" are to be noted.

A lot of spam in text format with dodgy language are a sorry sight indeed, but the spammers have learned and use images in the emails that are pulled from the web sites they impersonate being sent from.
By simply hovering over the links it becomes clear without a doubt when an email is spam.
The idea that Facebook would point to a Spanish website with link appearing to go to their website should convince any sane individual that they are looking at spam.
Only a spasm in the finger should get these links clicked...
 The Spanish site in question is most likely a victim of an intrusion where a redirect page placed by the spammer will catapult the unknowing visitor over to the spammer's web site of choice.
The Spanish site in question is most likely a victim of an intrusion where a redirect page placed by the spammer will catapult the unknowing visitor over to the spammer's web site of choice.
The Internet is littered with soiled web servers running unpatched software, root kits, or just simply without any security (essentially just pick one reason).
Add to it that these boxes run without very limited (if any) analysis of the log files providing an excellent breeding ground for all types of spam/malware/fake antivirus misuse. So what happens is that when either finger spasms occur or ignorant email recipients click on the links a redirect from the Spanish site happens, and the visitor winds up on yet another fake web pharmacy.
Call to action is for all owners of web sites to keep an eye on the volume of referrers, unexplainable increases means something is going down.

Despite the bashing of Alexa, on the accuracy of its data, it is quite useful on a global basis for checking out the rise and fall of spammer domains.
It seems the number of email recipients clicking on the links was quite large on this Facebook styled spam, note how the spammer domain managed to break the 60k line for a brief couple of days.
Perhaps the simple fact is that many Facebook users are gullible and not smart enough to spot a piece of spam...
A good sign is that the spammer website dropped dead as a door nail in a very short amount of time, reason unknown and the domain doesn't respond any more. Email recipients that are careful can easily spot spam a mile away, and a few simple checks will ensure that they are not being fooled to click on dodgy links.
Web site owners on the other hand need to be proactive in their log analysis, especially when unexplainable traffic increases occur. Add to that keeping the web server patched up to date and scanning the files of the website for unknown content will ensure that at least their web site isn't involved in illegal activity.
Spam 2.0 leads Facebook users to Canadian Pharmacy ring [DEAD LINK]